When it comes to SCADA security, hackers are everywhere. They’ve become so common that businesses make stopping them part of their everyday operations.
But when a cyber-attack is launched on a SCADA network, the potential consequences can be very serious—especially when it comes to vital public systems. In the most severe cases, security breaches can be fatal.
Today’s industrial infrastructure, from transportation to water and power applications and other critical infrastructure, is monitored and controlled by Supervisory and Control Data Acquisition (SCADA) software systems. It doesn’t take much of an imagination to realize the great damage that could be done to many SCADA-controlled systems if the network’s SCADA security is breached.
With the advent of SCADA networks featuring the latest Internet Protocol-based systems has come vulnerabilities to their security.
Legacy SCADA Systems
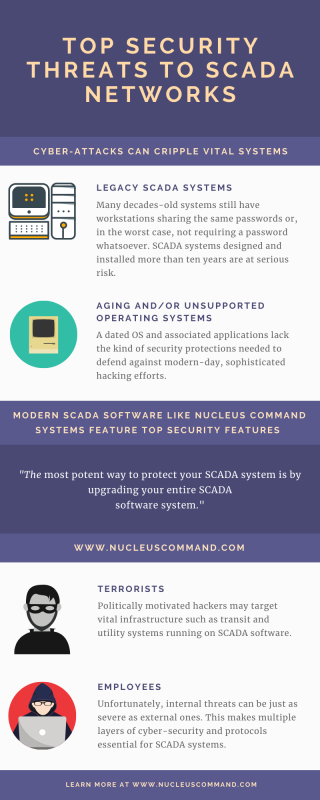
One of the most vulnerable areas of the SCADA security world are legacy systems. These were designed and built for critical infrastructure before cybersecurity was a major concern. It is common to find vital systems for municipalities such as water/waste water to be run on SCADA software that simply doesn’t have the modern protocols and processing necessary to operate adequate encryption and authentication processes.
As one cybersecurity firm has noted, “What were once systems that used relatively harmless proprietary protocols evolved into internet protocol (IP)-based systems that inherited all the vulnerabilities associated with the IP protocol.”
Believe it or not, there are systems in operation today (that shall remain anonymous for security reasons) that still have workstations sharing the same passwords. Or, in the worst case, systems do not require a password whatsoever. If your SCADA system was designed and installed more than ten years ago you could be at serious risk. Should your system come under attack, your network would be essentially bringing a knife to a cyber gun fight.
According to Automation IT, legacy SCADA systems “are now becoming less able to support new safety and data processing requirements along with being at high risk of failure at any moment, so are now a major liability and the cost to asset owners can be much greater than they realize.”
Beware of Old Operating Systems & Applications
Is your SCADA network running on the Windows XP operating system? If so, your system is the cyber-security equivalent of a four-alarm fire. Why? Microsoft has not supported XP (and previous versions) for several years. The same issue arises from affiliated applications such as SQL servers that are outdated and thus easily breached. The fundamental OS and associated applications lack the kind of security protections needed to defend sophisticated hacking efforts.
Malware Can Target Mobile Devices
If you’re not familiar with the damaging effects of malware on networked systems, you should be. Malware (malicious software) is a broad term used to describe any range of viruses, spyware or ransomware written to disrupt. These malware try to steal data, damage/destroy systems, or simply cause disruption or destruction of devices and systems.
Typically, malware has a difficult time invading the network itself (assuming it is protected). But often times these malicious bugs will target more vulnerable areas such as mobile SCADA applications that manage SCADA systems.
Protecting SCADA Systems
The most potent way to protect your SCADA system is by upgrading your entire SCADA software system. Most latest SCADA platforms, such as Nucleus, which safely and securely operates major urban transit systems every day as well as other industrial applications, offer protection that older systems cannot. So when considering an upgrade of your SCADA system, experts recommend that cybersecurity be among the highest priorities when choosing a SCADA software for a control system.

